MISP Maltego Versions Save
Set of Maltego transforms to inferface with a MISP Threat Sharing instance, and also to explore the whole MITRE ATT&CK dataset.
v1.4.5
4 years agoSearching with % wildcards
While the Galaxies already supported sub-string search this feature is extended to all the supported Maltego entities. From now you can use the Search in MISP transform on any Maltego entity.
As with the MISP attribute search through the MISP Web UI you can use % wildcards at the front and end to specify the substring. You might be tempted to always use %keyword%, but bare in mind how databases indexes work; a search for keyword% will always be much faster than %keyword.
Massively large MISP event? Think before you transform.
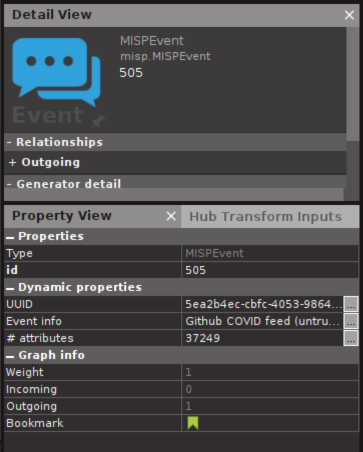
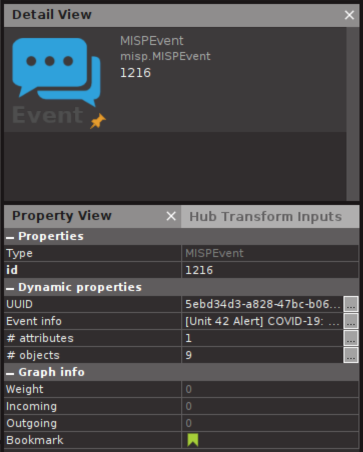
In some communities such as the COVID-19 MISP some events contain tens of thousands attributes. Loading all the attributes from these events might not be a good idea if you do not have Maltego XL.
From now on you can see the amount of attributes and objects in the Event properties, so you can think before you click:
Various improvements and security fix
This release resolves an information disclosure vulnerability when using MISP-maltego as remote transform server. The transform server would cache the MISP credentials of the first user connected, and provide access to that MISP instance for any later user. (CVE-2020-12889).
This release also brings various improvements:
- Tag to Event massive performance boost
- Minor fixes in Machines who were not working as expected
- Minor code cleanups
v1.4.4
4 years agoObject icons
MISP objects are in addition to MISP attributes to allow advanced combinations and concatenation of attributes. The creation of these objects and their associated attributes are based on real cyber security use-cases and existing practices in information sharing. For example a File will contain various type of hashes; an Email will have a sender, recipient, content, headers, and attachments.
Before this release MISP-maltego showed all objects in the same way: a file, email, imsi-catcher and person had the same icon:
![]()
With this release this improves considerably and provides a much better visual experience to the analyst. About 50 object types are currently supported in the new icon mapping.
![]()
Various improvements
This release also brings various smaller improvements and bug fixes:
- Fixing issue #23 where the local galaxy cache can get corrupted when two process try to download the cache at the same time.