Pe Sieve Versions Save
Scans a given process. Recognizes and dumps a variety of potentially malicious implants (replaced/injected PEs, shellcodes, hooks, in-memory patches).
v0.2.9.8
2 years ago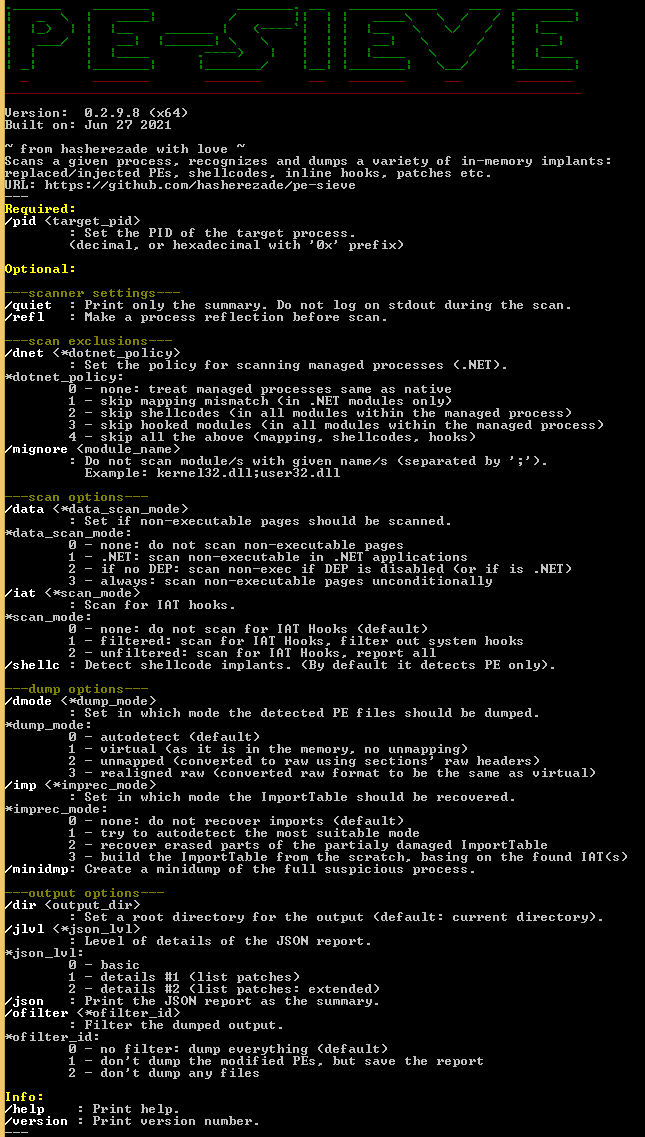
FEATURE
- added a new pattern for detecting 64-bit shellcodes
- added return codes informing about the result of the run
- removed unused parameter :
/mfilter - in JSON: added an indicator if the replaced module was linked to the PEB
BUGFIX
- Fixed error in dumping some of the PEs (issue caused by the invalid ImageSize calculated: Issue #85)
v0.2.9.6
3 years agoFEATURE
- in JSON: report the size of the patch, status, as decimal (rather than hexadecimal)
BUGFIX
- Fixed crash on processing a malformed export table (Issue #84)
v0.2.9.5
3 years agoFEATURE
- Improved parameters accessibility: grouped into more categories, sorted.
- Display hints for misspelled parameters
- Added parameter
jlvlallowing to regulate the level of details included in the JSON report. Allow to list hooks/patches in thescan_report. - Improved hook parsing: identify hooks created by replacing the target of existing JMP/CALL
BUGFIX
- Improved reading remote memory (fixed a bug that was causing PE-sieve to stuck in some cases of reading inaccessible memory)
- Do not include initial protection in the check of memory access rights
v0.2.9
3 years agoFEATURE
- In DLL: use
__cdeclcalling convention (instead of__stdcall) - In case if scanning data is enabled (
/dataparameter) scan for hooks also the sections that are marked as non-executable (if they contain code patterns) - Added a count of sections scanned for patches to the report
BUGFIX
- Fixed a bug in detecting a section with Entry Point (affecting unpacking of some packers, such as ASPack - Issue #73 )
- Fixed bug in libPEconv: do not treat empty relocation blocks as invalid
REFACT
- Some internal cleanup and refactoring
v0.2.8.6
3 years agoBUGFIX:
- Fixed error in scanning workingset of some applications (Issue #68)
v0.2.8.5
3 years agoBUGFIX
- Fixed broken detection of ASProtect ( Issue #66 )
- Fixed broken parsing of a hexadecimal PID ( Issue #65 )
- Fixed errors on code scan (caused by invalid relocation table check)
- Do not assume that the section 0 is always executable
- Fixed bug in scanning 64bit modules by a 32bit scanner
FEATURE
- Added one more pattern to detect 64 bit code
REFACT
- Refactored identifying executable sections
v0.2.8.3
3 years agoBUGFIX
- Fixed hanging during the IAT scan of some PEs
- Fixed error in converting paths from the
/Device/format - Fixed not listing results of the mapping scan in the summary
FEATURE
- added one more .NET policy (in
/dnetparameter) - In the summary: changed
detachedtounreachable_file
v0.2.8
3 years agoFEATURE
- Detailed info about a single parameter can be requested by:
/<parameter> ? - New modes in the
/dataparameter - New parameter
/dnetallowing to enable treating .NET modules differently than native ones - Report about PE implants and shellcode implants separately
- Added information in the report: process bitness, is process managed (vs native)
- Minor changes in the API:
PEsieve_versionimplemented as a constant - Allow for partial scanning of 64 bit processes by a 32 bit scanner
BUGFIX
- If the parameter
/reflchosen, the process reflection should be used for both scan and dump - Fixed switching back to the original console color after printing in color (improved look on Powershell console)
- Fixed recognizing if the PE in the memory is in raw or virtual mode (it was giving invalid results for some payloads)
- Fixed broken parameter
/mfilter
REFACT
- Refactored parsing of the parameters
- Internal refactoring and cleanup of the scanner
v0.2.7.1
3 years agoFEATURE
- Scan virtual caves
BUGFIX
- Fixed
/mginoreoption (filtering out selected modules from the scan) - Fixed wrong calculation of a patch size
v0.2.7
3 years agoFEATURE
- New parameter:
/reflallowing to make a process reflection before scanning - Support scanning PEs with no sections (i.e. packed with Crinkler) (Issue #46)
- Allow to build as static library
- Dump report about hooks even if dumping the modules failed
- Show the time of scanning workingset
BUGFIX
- Fixed JSON in code scan report (in case of reporting errors)
- Fixed problems with dumping PEs with bogus Image Size (prevent crashes, try to autodetect the correct size)
REFACT
- Internal refactoring (i.e. in scanning workingset)
- Set debug privilege unconditionally