Il2CppInspector Versions Save
Powerful automated tool for reverse engineering Unity IL2CPP binaries
2021.1
3 years agoWe Inspected (almost) Everything.
Il2CppInspector 2021.1 brings an avalanche of new features and bug fixes, with a focus on enabling as many IL2CPP applications as possible to be analyzed.
In addition, Perfare - author of the popular Il2CppDumper tool - has asked us to port some features of Il2CppDumper over to Il2CppInspector in order to create a single unified tool going forwards. This release brings Il2CppInspector to feature parity with Il2CppDumper in addition to all of the pre-existing extra functionality, with the exception of WebAssembly and NSO file format support (coming soon).
Major new features:
-
Plugins: You can now create plugins that allow you to completely edit the load pipeline and implement custom deobfuscation, decryption, perform additional analysis and generate additional outputs.
This enables you to write standalone code for specific workloads without needing to fork and edit the source code of Il2CppInspector, and your code will continue to work when we release new updates.
We're really excited about this new feature and have created a Plugin Wiki with information to help you get started writing your own plugins. We've also created many example plugins you can check out to learn more! You can also submit your own plugins, and we will bundle the current set of plugins with each new release.
-
DLL output support: You can now output assembly shim DLLs that are semantically compatible with those produced by the "dummy DLL" function of Il2CppDumper. This is a complete rewrite of Il2CppDumper's DLL output using dnlib and Il2CppInspector's type model, and brings the following enhancements:
- Orphaned property methods are now handled correctly
- Events are now handled correctly
-
reftype method parameters are now output correctly - Static field offsets are now output (
StaticFieldOffsetattribute) - Assembly-level attributes are now output for each assembly
- Assembly and module metadata tokens are now output
- Attributes with zero arguments are applied directly rather than via the
Attributeattribute for improved readability - Static array initializers include an 8-byte preview of the array contents (
MetadataPreviewattribute) - The generated output is self-contained with no external references to
mscorlib.dll- this means the generated DLLs can be used with Il2CppAssemblyUnhollower without modification even on .NET Core - You can now suppress all output of all metadata attributes (use
--suppress-dll-metedataon the CLI or the corresponding GUI option) - handy if you just want to browse or compare the raw type definitions
-
Dumped memory image support: memory dumps can now be loaded and rebased (use
--image-baseat the CLI or Import Options in the GUI to specify the image base address) -
GameGuardian dump / Linux process map support: you can load a GameGuardian dump or Linux process map without needing to split or extract
libil2cpp.sofirst or know the image base address. Specify the*-maps.txtfile in place of the binary file and Il2CppInspector will reconstruct and rebaselibil2cpp.sofor you
-
Automated deobfuscation:
-
The new Beebyte Deobfuscator is our first 3rd party plugin and can deobfuscate .NET type and field names when supplied with an earlier, unobfuscated version of the same application by performing a differential analysis and applying renaming to the obfuscated version. The unobfuscated input can be either an IL2CPP or Mono build. You can also optionally output a text file containing a list of name translations, or a plugin source code file for use with Il2CppTranslator
NOTE: You MUST supply an unobfuscated (or less obfuscated) version of the application in order to perform automatic deobfuscation!
NOTE: This plugin is still a work in progress and may contain bugs. Properties and method names are not currently deobfuscated.
-
Most types of packed PE files (Windows DLLs) can now be loaded automatically (eg. Themida DRM)
-
Automatic reconstruction of the correct field order for
Il2CppCodeRegistrationandIl2CppMetadataRegistrationin most cases where it has been obfuscated (eg. Riot Games workloads) -
Automatic decryption of XOR-encrypted .NET symbols
-
More sophisticated heuristics are now used to determine binary file XOR keys and block sizes, this should improve compatibility with some encrypted workloads (eg. Arknights, Call of Duty Mobile, Garena Free Fire + many others)
-
Automatic binary XOR decryption now also works on 64-bit (ARMv8) binaries
-
ROT-encrypted API exports will now be resolved automatically (eg. Legends of Runeterra, League of Legends Wild Rift)
-
Honkai Impact and Genshin Impact can now be loaded using the miHoYo plugin (bundled) (you must supply a
UnityPlayer.dllfrom a matching version, even if analyzing a mobile release) -
Tale of Immortal (鬼谷八荒 / Guigubahuang) can now be loaded using the guigubahuang plugin (bundled)
WARNING ON THE USE OF AUTOMATIC PE UNPACKING: Loading a packed PE file enables arbitrary 3rd party code execution. Do not load potentially malicious DLLs and never run Il2CppInspector as an administrator when handling packed PE files. USE AT YOUR OWN RISK.
PLEASE NOTE: We will not be providing deobfuscators for every workload; the functionality above is provided by plugins for example purposes and we recommend you use the provided APIs to write your own plugins if you need to analyze an application not directly supported by Il2CppInspector. We do not take requests - please do not file issues asking for specific applications, they will be ignored.
-
-
Tutorials and guides: We've published a tranche of new guides for you:
-
IL2CPP: IL2CPP Reverse Engineering Part 2: Structural Overview & Finding The Metadata
-
Il2CppInspector: How to create, use and debug IL2CPP DLL injection projects
-
Il2CppInspector: Working with code in IL2CPP DLL injection projects
-
Walkthrough: Enable loading of League of Legends: Wild Rift - covers XOR decryption, XOR string decryption, API export ROT decryption, data obfuscation of binary metadata
-
Walkthrough: Enable loading of Honkai Impact (3 parts) - covers finding functions in an image, data obfuscation of global-metadata.dat, IDA decompiler techniques, how to write a plugin
-
Walkthrough: VMProtect control flow obfuscation in Honkai Impact - covers extrapolating the code path from a function with control flow flattening using x64dbg and the IDA decompiler
-
Walkthrough: Reverse engineering Genshin Impact with PowerShell - covers writing a test harness to find a function in an obfuscated binary via brute-force attack / reverse fuzzing
-
Minor features:
-
XAPK package files are now supported
-
ZIP files containing APKs are now supported directly
-
You can now save extracted, decrypted or deobfuscated
global-metadata.datand binary files via the CLI or GUI (use--metadata-outand--binary-outat the CLI) -
You can now specify a Unity asset file to give Il2CppInspector the precise Unity version used, rather than specifying the version by hand or letting Il2CppInspector guess. This can be used to improve the accuracy of some types of output (use
--unity-version-from-assetat the CLI or Get Unity version from asset file... in the GUI) -
We hired someone who can use Paint to make an application icon for Il2CppInspector's GUI, yay!
-
We hit some things with a hammer and some types of file will now load much faster - huzzah!
Minor improvements:
-
C++:
enums will now be output asenum classes for scaffolding projects -
C++: Scaffolding projects have
il2cpp_thread_attach(il2cpp_domain_get())added to the start ofRun()to prevent fatal unmanaged exceptions when calling certain methods -
CLI: You can now select individual outputs by specifying
--select-outputs; this will cause all outputs to be suppressed except those you specify as arguments. The default is still to output everything - IL2CPP: Archive files won't be read-locked when loading anymore, allowing you to run Il2CppInspector when they are open elsewhere
- Type model: Removed no longer necessary thread locking when generating custom attribute data
Notable bug fixes:
- C#: Fix failure to generate class/tree folder layout when there are invalid namespace names
-
C#: Fix assembly type indices were still being emitted when
--suppress-metadatawas specified -
C#: Fix crash outputting 64-bit
Flags-style enums with the top bit set -
C++: Signed
enumtype output did not match theenums underlying type -
C++: Signed
enumvalues that are negative will no longer be output in hexadecimal - C++: Fixed a compilation error in scaffolding projects "fields is not a member of app::String" for certain IL2CPP applications
- Formats/ELF: Don't crash trying to fetch a section by name that doesn't exist
- Ghidra: Dumped ELF images were not rebased correctly
- GUI: The GUI won't crash silently on startup anymore if an error occurs
- IDA: Fixed "abstract declaration is not allowed here" error when parsing C headers for certain IL2CPP applications
- IDA: Fixed "SetType failed!" error when applying script to an IDB where some duplicate types already exist
-
IL2CPP: Fixed an edge case causing a rare crash when analyzing
metadataUsageslist -
IL2CPP: Fixed an edge case causing a workload with an unusually large number of
reversePInvokeWrappersto fail to load - IL2CPP: Fixed method pointer offsets output being off-by-1 in certain types of non-PE x86/x64 binaries
- Type model: Fix crash that occurred on invalid/obfuscated assembly or namespace strings
- Type model: Fix crash that occurred when resolving generic type arguments in 32-bit binaries that have been rebased
-
Type model: Fix
GetType()andGetGenericMethod()incorrectly returnednullwhen searching for a type or method in the global namespace - Unity: Fix crash comparing Unity versions when one of the version ranges is open-ended (caused crash on the latest Unity releases)
- ...and more
Unity support:
- Support was added or tested where applicable for Unity versions up to Unity 2018.4.31, Unity 2019.4.18 and Unity 2020.2.2 (the current latest)
New APIs for developers:
-
Formats:
FileFormatReaderclasses can now receive aLoadOptionsargument with custom load options -
Formats: Added
FileFormatReader<T>.DefaultFilenameto fetch the default filename for a given file format -
Formats: Added
Sectionclass andIFileFormatStream.GetSections()/IFileFormatStream.TryGetSections()for universal processing of sections regardless of file format (ELF files will use the PHT if the SHT has been destroyed) -
Formats: File types can now have multiple "load strategies" which will be tried in sequence once the file format has been identified (eg. unpacked, packed); see
IFileFormatReader.TryNextLoadStrategy() -
IL2CPP:
MetadataandIl2CppBinarynow derive from the newBinaryObjectStreamallowing easy reading and writing of types to the underlying streams -
IL2CPP: Added
IsModifiedproperty toMetadataandIl2CppBinary -
IL2CPP: Added
Il2CppBinary.SaveToFile(),Metadata.SaveToFile()and equivalent surrogatesIl2CppInspector.SaveBinaryToFile()andIl2CppInspector.SaveMetadataToFile()to enable saving of modified files -
Plugins: An entire new API set was created for plugins, and many previously
privateorinternaltypes, fields and properties were madepublic. See the Il2CppInspector Plugin Wiki for full details. Users developing standalone apps using the Il2CppInspector API can disable the entire plugin system withPluginManager.Enabled = false -
Type model: A small number of
MemberAttributesflags that were omitted are now included (eg.FieldAttributes.RTSpecialName).PropertyAttributesandMethodImplementationFlagswere added as per the .NET Reflection API -
Type model:
MetadataTokenwas added to all type model objects as per the .NET Reflection API - ...and more
We're going to take a little break now, but we'll be back in May to cause more trouble (critical bug fixes will still be posted). Happy hacking!
Many thanks to @std-nullptr, @Perfare, @OsOmE1, @cctgapp, @AndnixSH, @MerzZly, @badluck13, @rustyx, @RaenonX and everyone else who provided input and contributions to this release!
2020.2.1
3 years agoIl2CppInspector 2020.2.1 is a minor feature update and maintenance release, containing dozens of bug fixes and small improvements.
-
Universal IL2CPP Build Utility: The old binary generator script has been replaced with a significantly revamped build utility for PowerShell -
il2cpp.ps1. Type./il2cpp.ps1 -helpfor usage instructions- The Roslyn C# compiler will now only be invoked for the specified files, rather than all source files in the folder
- You can now specify which installed Unity version to use as the build target. This allows wildcards, so
2019.3*will use the latest install of Unity 2019.3 etc. - You can also optionally specify a full Unity path as the version argument to bypass the automatic installation search; this also supports wildcards
- The Unity bytecode stripper will now be run on each assembly before being transpiled to reduce the total build time
- Each assembly will now only be transpiled to C++ once, rather than once per architecture target (this was wasteful as the C++ code doesn't change)
- The build cache will now be created in a child folder of the output folder and deleted upon completion (previously it would be in the user's Temp folder and not deleted before a reboot, causing the rapid consumption of disk space when performing many builds)
- Fix for the
MapFileParser.exepath not being passed toil2cpp.execorrectly - Android builds will be skipped rather than aborting the whole script if the Android toolchain is unavailable
- The Cpp source folder will be wiped before a re-build to avoid conflicting source files
- The utility will now work on all versions of Unity from 2017.1.0 - 2021.1.0+ (previously only supported Unity 2018.3.x - 2019.3.x); please see the source code comments for build tool requirements and other dependencies for the different Unity versions
- The utility is now compatible with PowerShell 7 (previously only 5.1)
- Various bug fixes
-
Android file format improvements: Split APKs and AAB (Android App Bundle) files are now supported via the API, CLI and GUI
-
Breaking change to C++ scaffolding: All
__TypeInfovariables are now double-indirected rather than single-indirected pointers. You will need to update your projects to take this into account.
Improvements:
-
C#: Static array initializers (ie.
PrivateImplementationDetails) now show an 8-byte preview of the array and the offset intoglobal-metadata.datof the whole array - C#: The generation of type definitions is now parallelized giving a substantial speed up
- C++: Allow the parsing of enums with negative values
- C++ scaffolding: All IL2CPP surrogate versions of .NET managed types are now included in the output headers, giving access to many more important types
-
C++ scaffolding: All types from
vm/MemoryInformation.hare now included in the output headers -
C++ scaffolding: All
MethodInfopointers are now available via the new<method-name>__MethodInfovariables (double-indirected pointers) -
C++ scaffolding: The helper API names were refactored to start with
il2cppi_ -
C++ scaffolding:
il2cppi_to_string()added to convertIl2CppString*andapp::String*tostd::string -
C++ scaffolding:
il2cppi_is_initialized()added to allow you to check if a metadata item (TypeInfo,MethodInfoetc.) is initialized before using it -
C++ scaffolding: The IL2CPP metadata version is now defined in
il2cpp-metadata-version.h -
C++ scaffolding: The contents of
userfolder will now be preserved, allowing you to re-build scaffolding in-place when the target application is updated without losing your work - C++ scaffolding: Projects can now be built with Visual Studio 2017 as well as 2019 (some API features will be disabled)
- Formats/ELF: Dramatic speed up when processing encryption
- Formats/ELF: Handle striped XOR encryption
- Formats/MachO: Dynamic libraries and other non-executables will now be accepted
- Formats/PE: Auto-detect binaries packed with Themida and others and give a descriptive error message (Note: an unpacker will be added in a future update)
-
Ghidra: C++
enums with a derived type can't be parsed by Ghidra; now we output C-styleenums instead. Fields instructs which have a C++enumtype that has an underlying type with a memory size different touint32_twill be replaced with a non-enumfield of the correct size to maintain an accurate memory layout of thestruct - Ghidra: Ghidra script will now prompt you if you forget to parse the C headers before running the script
- GUI: Select All / Select None buttons added to the namespace tree selector
- GUI: More descriptive progress updates while analysing files
- GUI: The 'Building application model' phase will be skipped if it has already been built with the same parameters
- IDA: Python 3 support added for IDA Pro 7.4+
- IDA: The placement of function boundaries is now more accurate
-
IDA/Ghidra:
Il2CppCodeGenModulearray (g_CodeGenModules) is now typed -
IL2CPP: Auto-detect re-arranged fields designed to obfuscate
Il2CppMetadataRegistrationandIl2CppCodeRegistrationand give a descriptive error message - IL2CPP: Handle files using metadata v24.4 (2019.4.15+ and 2020.1.11+)
- Unity: Existing headers updated and new headers added for 2019.4.15 and 2020.1.5+
- ...and more
Bug fixes:
- C#: Fix indexer names were corrupted if the name length was not exactly 4 characters
- C#: Type, method, parameter, field and event names could contain invalid characters
- C#: Unicode characters in identifiers are now handled correctly
-
C#: Scoped names referencing the global namespace (
global::) are now handled correctly -
C#:
floats anddoubles could be output with the wrong decimal separator when using a non-English locale - C#: Fix for invalid characters in generic types that use other generic types as their type parameter(s)
-
C++: Unused concrete value types were incorrectly omitted from
il2cpp-types.h - C++: Unicode characters in identifiers are now handled correctly
-
C++ scaffolding:
init_il2cpp()would sometimes populate__TypeInfovariables with zero if not all of the IL2CPP application types have been initialized wheninit_il2cpp()is called, causing a crash when creating new objects. This was solved via the breaking change above - C++ scaffolding: Compiler warning 4359 when compiling for 32-bit architectures
- C++ scaffolding: 32-bit Debug build was misconfigured
- Formats: Fix crash reading certain types of files with 0-length arrays mapped to virtual addresses
- Ghidra: Ghidra script is now compatible with Ghidra 9.2
-
Ghidra:
structs with fields called_extensionwould fail to parse -
Ghidra:
structs with self-referential fields would fail to parse - IDA: Fix failure to process C header if the script and binary folders are not the same
- IDA: Fix additional reserved keyword naming conflicts
- IDA: Worked around a bug in IDA causing leading underscores to be removed from parameter names if present
- IL2CPP: Assemblies containing only interfaces, abstract methods or open generic methods will no longer cause a crash
- ...and more
API-only NuGet install: search for NoisyCowStudios.Il2CppInspector from the NuGet Package Manager.
The next release will continue to focus on improvements and bug fixes to C++ scaffolding, which is still early in its life!
Enjoy the update and happy hacking!
Thanks to @eliphatfs, @anonymous1753, @kotori2, @lifeengines, @exp111, @cctgapp, @ianpei, @jakecrowley, @pandaboy1942, @camas, @Warpten, @AxelHu, @CiberBot13, @shazgames, @MerzZly, @vfsfitvnm, and of course, the ever-present @DannyParker0001 for their input and contributions to this release!
2020.2
3 years agoHold onto your disassemblers, IlCppInspector 2020.2 is here to get up in your business and steal yo' girl!
This release contains a slew of major new features:
-
New C++ scaffolding header generation: In addition to the existing scaffolding, Il2CppInspector now outputs C++
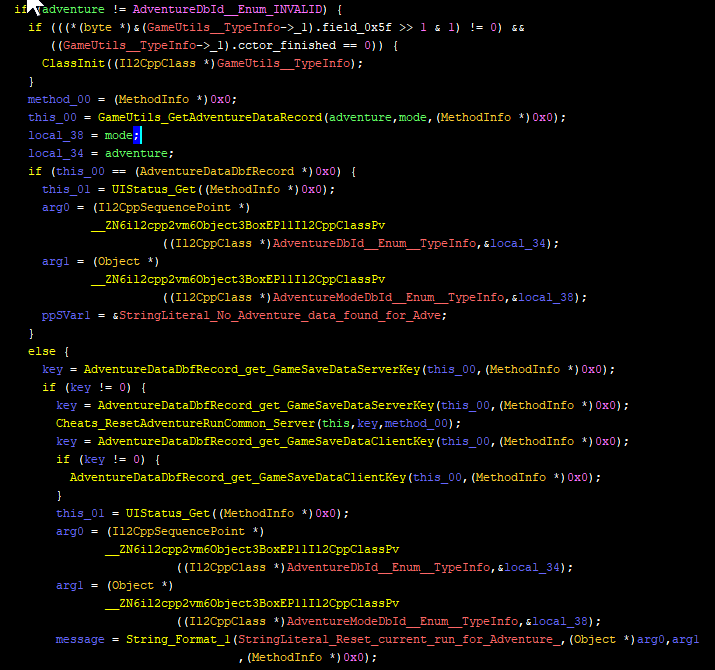
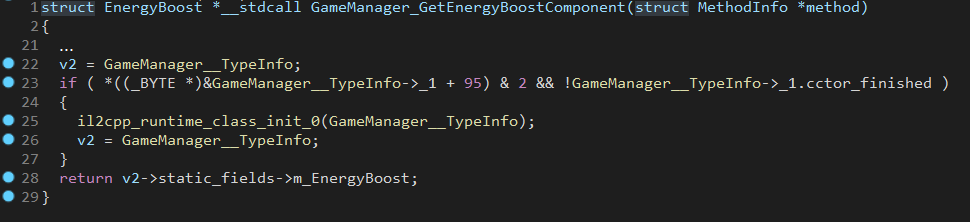
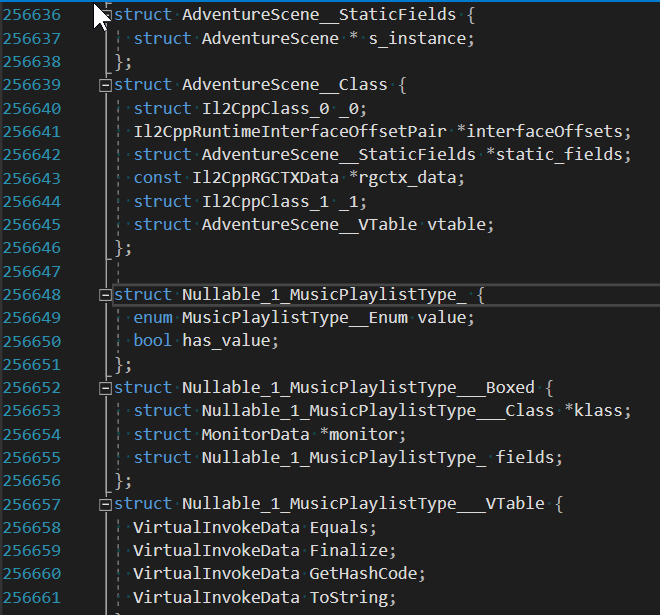
typedefsignatures and pointer base offsets for every function pointer in the application - for both .NET methods and IL2CPP APIs - plus pointers to every type definition (Il2CppClass *) in the binary. This works on Windows, Android and iOS (include theappdataheaders with your project for eg. Cydia Substrate) - no more searching through files for function pointers and writing your own definitions! This means you can now write code like this:/ Use IL2CPP API and an Il2CppClass* to create a .NET-mapped object ector3__Boxed* myVector3 = (Vector3__Boxed*) il2cpp_object_new((Il2CppClass*) Vector3__TypeInfo); / Call a constructor on an object ector3__ctor(myVector3, 1.0f, 2.0f, 3.0f, NULL); / Access an instance field of an object loat y = myVector3->fields.y; / Access a static field of an object uto playerHealth = GameManager__TypeInfo->static_fields->m_PlayerHealth;This code will work in any IL2CPP application - no need to know the binary layout, just re-run Il2CppInspector to produce new C++ scaffolding for each new application or patch and all the addresses and offsets will be adjusted for you without having to change your code!
Il2CppInspector will also handle binaries with partial or no API exports by using heuristics to match the found functions to the closest Il2CPP API version possible, and omitting missing API calls from the C++ output.
-
Visual Studio DLL injection projects: Il2CppInspector can now automatically generate a complete DLL injection project and Visual Studio solution for Windows IL2CPP applications, using all of the scaffolding above plus a ready-made DLL template. Just edit
main.cppwith your desired code, compile, load it into a DLL injector such as Cheat Engine and you're good to go! -
Full Ghidra support: Not just names and labels, but fully typed functions and decompilation plus the exact same set of rich metadata output for IDA users is now available for Ghidra! (make sure to check the tutorial in the README to see how to use this)
-
Application Model API: Complementing the existing .NET type model, the AppModel allows you to query every part of an IL2CPP application programmatically, providing composite mappings between .NET and C++ types and methods, all of the C++ classes and functions used in the application with complete field and type information, non-.NET functions such as custom attribute generators, Method.Invoke thunks and typed IL2CPP APIs, as well as centralized access to versioned Unity headers, string literals, all of the binary's symbols and exports and any known metadata references.
-
Address Map (experimental): Building on the AppModel API, you can now query any virtual address in the IL2CPP binary and retrieve information about the address contents, including any .NET mappings if applicable. All of the information managed by the AppModel API is also available in the Address Map.
-
IDA functionality enhancements: Il2CppInspector now generates type signatures for
CustomAttributesCacheGeneratorandMethodInvokerfunctions, instead of just labels. Plus, detected IL2CPP API exports with known function signatures will now also be converted into typed functions (these improvements are also included in the Ghidra support) -
JSON metadata output: You can now generate the same data provided to IDA and Ghidra as a JSON file (in fact, this file is now used by the disassembler scripts), allowing you to query it from other applications (Note: there is a huge amount of metadata available and only a fraction of it is output; edit
Outputs/JSONMetadata.csto add more details) -
NuGet package: Il2CppInspector's API components are now available on NuGet! Just install
NoisyCowStudios.Il2CppInspectorfrom the NuGet Package Manager. -
Tutorials and guides: We're slowly building a library of articles on how IL2CPP works, and practical guides on using Il2CppInspector to solve real-world reverse engineering problems. Check out this guide on Using Il2CppInspector's type model to extract protobuf-net definitions (using the game Fall Guys as a case study) - more guides are on the way!
Minor features:
-
Multi-architecture APK files are now supported. If you import an APK with multiple IL2CPP binaries, all of the binaries in the package will be analyzed.
-
The GUI now has drag & drop support for all supported file formats. You can also drag a metdata and binary file together!
-
A third method to find the required metadata: Il2CppInspector has previously looked at the symbol table - and if that failed, disassembled parts of the code - to find the needed data to inspect the binary. It can now also brute-force scan the data of the binary looking for this data if the first two methods fail. This improves detection on dumped files and binaries with non-standard compilation.
-
Python script target extensibility: You can now add support for other disassemblers or script targets by implementing a simple single-file Python API - see the README for details
-
Minor improvements to C# code stubs output (async methods now get the
asynckeyword;[DefaultMemberAttribute]is no longer suppressed if a type doesn't have an indexer) -
Manipulating binary files directly from code has had a number of convenience features added (see
FileFormatReaderclass)
Other notable API enhancements:
- You can fetch all of the IL2CPP API exports in a binary using
Il2CppBinary.GetAPIExports(), and all of the available typed IL2CPP API exports available both in the binary and corresponding Unity headers withAppModel.AvailableAPIs - You can now fetch the machine code for custom attributes generators and method invokers with
GetMethodBody()in the same way you already can for .NET methods - Silent analysis options
- ...and many more not listed here
Unity support:
- Full Unity 2020.1 support: Unity 2020.1 introduced changes to the initialization code and is now supported
- Full Unity 2020.2 (alpha) support: Unity 2020.2 introduces significant changes to metadata usage references - making it necessary to use heuristics to locate this data - plus small changes to custom attributes generators and generic class references. But don't worry, we've got your back! Il2CppInspector 2020.2 provides the exact same feature set for Unity 2020.2 as every other version of Unity (including C++ header output).
- Support was added or tested where applicable for all Unity LTS versions up to Unity 2018.4.26 and Unity 2019.4.8 (the current latest)
Notable bug fixes:
- Visual Studio solution generation now works on MacOS X
- Fixed a fatal crash in Unity version parsing when using Il2CppInspector with a non-English locale
- The image suffix digit was only applied to the C# code stubs output and no other outputs, causing them to be overwritten when using the CLI with a multi-image binary
- Fixed two GUI crashes when working with multiple IL2CPP applications in one session
- C++ scaffolding for Unity 5.3.6-5.4.6 would not compile due to a missing
struct VirtualInvokeDatadefinition - Fixed the C++ signatures in IDA output for MethodInvokers for Unity 5.3.0-5.6.7
- The signature for
il2cpp_codegen_registerwas incorrect for Unity 5.3.4 and lower - The C++ scaffolding for
System.Arraywas incorrectly output as an array instead of a class - Field offsets in C++ structs were calculated incorrectly in some cases
- ...and more
Enjoy the update and happy hacking!
Thanks to @DannyParker0001 and @vivalavladislav for their contributions to this release!
2020.1
3 years agoIl2CppInspector 2020.1 delivers dozens of improvements including several major new features:
-
IDA functionality enhancements: Il2CppInspector now outputs type declarations for all IL2CPP internal types and types used by the application, including all generic instances, plus address mapping for every type definition and method argument types. Boxed types are generated as required. Memory-mapped vtables are generated for every type. Function boundary mapping has also been improved.
-
C++ scaffolding output module: You can now output C++ headers with type declarations for all IL2CPP internal types and types used by the application, including all generic instances and inferred usages from metadata, plus all vtables and applicable boxed types. You can select which C++ compiler to target for the output (MSVC or GCC). Perfect for use with x64dbg among others!
-
Native APK and (decrypted) IPA support: You can now specify an APK or IPA file on the command-line or via the GUI - Il2CppInspector will automatically unzip the package into memory and locate the IL2CPP component files for analysis - no need to find the binary and metadata files first!
-
Generic types overhaul: This is a complete overhaul to the management of .NET generic types, improving the completeness and accuracy of all outputs (C#, IDA, C++). All closed generic types including those not defined directly but referenced by types or methods in the application are now accounted for. Nested and inherited open and closed generic types are handled correctly. New APIs are available for inspecting generic types.
-
Battle-hardened: Il2CppInspector is now compatible with all 205 releases of IL2CPP from Unity 5.3.0 to 2019.4.2+. For IDA and C++ outputs, Il2CppInspector will attempt to auto-detect both the Unity version and C++ compiler used to generate the IL2CPP application and generate a complete set of type definitions for the corresponding Unity version with the corresponding compiler-defined memory layout. You can override these options if you wish. Il2CppInspector will also perform automatic name conflict resolution to avoid the use of pre-defined symbols and keywords in C++, and to handle re-definition of same-named symbols in the application.
-
Many new API calls for the package (
Il2CppInspector) and .NET type model (Il2CppModel) for automated analysis of IL2CPP applications (see the source code for details; these are primarily for the handling of generic types and C++ declarations; you can now also useMethodBase.GetMethodBody()to retrieve the executable machine code for any method) -
Many bug fixes for IL2CPP processing
-
Minor improvements to C# prototypes output
-
Minor improvements to ELF handling and de-obfuscation
-
Using the
generate-binaries.ps1script now allows you to examine the generated C++, not just the final IL2CPP binary -
Output paths now work correctly for Linux and other POSIX filesystems
We're already working on some exciting new features for the next version, and hope you enjoy this update!
Thanks to @AntyMew , @carterbush and @nneonneo for their contributions to this release!
IDA C++ decompilation example:
C++ scaffolding example:
2.1
4 years agoIl2CppInspector 2.1 brings initial compatibility for PlayStation 4 .prx files and various fixes to support to IL2CPP applications compiled with Unity 2019.3, as well as compatibility with a broader range of x64 binaries.
ChangeLog from 2.0 to 2.1:
- Initial support for Sony PlayStation 4 FSELF (PRX) files (NOTE: PS Vita is not currently supported)
- Improvements to x64 binary analysis in multiple scenarios
- Unity 2019.3 compatibility fix for 32-bit ARM binaries
- Minor improvements to ELF handling
- Minor improvements to C# output
- Minor GUI improvements
2.0
4 years agoIl2CppInspector 2 is a complete overhaul of the original Il2CppInspector dumper tool, with massively improved usability and tons of new features, including:
-
Support for all IL2CPP versions from Unity 5.3 to 2020
-
Generates accurate well-formed C# code with syntactic sugar and language features up to C# 7.3
-
Generate stub code Visual Studio solutions (with .sln and .csproj files) including assembly references for your Unity install
-
The most detailed IDA script output available including full .NET method signatures, generic method instantiation and custom attribute support, plus support for Method.Invoke thunks, basic IL2CPP metadata structures and all available IL metadata
-
Customize your output: exclude unwanted namespaces, split types by assembly, namespace and/or class, produce a flattened set of files or folder hierarchy, sort types within files, separate assembly-level attributes into their own files, suppress metadata comments in C# code, and even attempt to produce code stubs that compile.
usingdirectives and scope resolution conflicts for each file are resolved automatically -
Enhanced file format support for PE32+, ELF64, Mach-O, multi-image Universal Binaries, relocations, symbol tables and more
-
New architecture support for ARMv8 / ARM64 (A64), Thumb-2 and x64. Enhanced support for ARMv7 and x86
-
An internal type model based on the .NET Reflection APIs allowing you to re-use a high-level representation of all IL2CPP data in your own applications using an already familiar API
-
Much more robust handling of nested types, generic methods, nested generic type references and derivations plus hundreds of other code output improvements and bug fixes
-
A brand new GUI for Windows users. The command-line tool is still available for Windows, MacOS X and Linux users.
-
Automatic processing of some very basic obfuscation
-
Integrated test suite. Each build is automatically tested on over 50 IL2CPP applications
I hope you enjoy the new version of Il2CppInspector!

1.0
7 years agoInitial release.