Hydra Versions Save
OpenID Certified™ OpenID Connect and OAuth Provider written in Go - cloud native, security-first, open source API security for your infrastructure. SDKs for any language. Works with Hardware Security Modules. Compatible with MITREid.
v2.2.0
2 months ago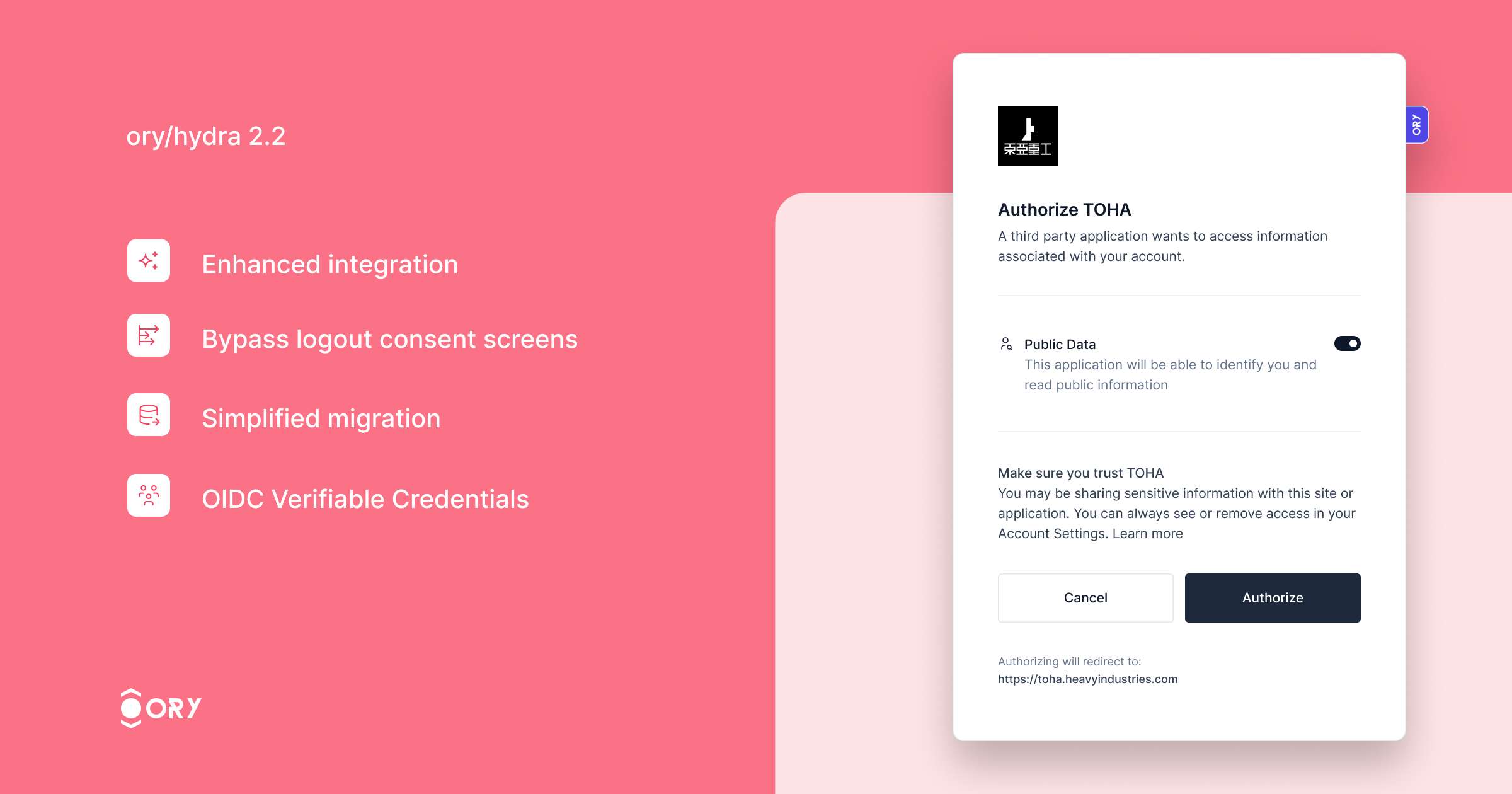
Ory Hydra, the OAuth2 and OpenID Connect server designed for web-scale deployments introduces over 6x higher OAuth2 throughput on a single PostgreSQL instance!
Want to check out Ory Hydra yourself? Try common OAuth2 flows in the Ory OAuth2 Get Started guide!
This version significantly enhances performance, processing over 6x more authorization flows than version 2.1, thanks to architectural improvements that minimize database interactions for login and consent processes.
Key improvements include:
- Enhanced integration with Ory Kratos, ensuring seamless synchronization of login and logout states across both services. Users logged out from Ory Hydra will automatically log out from Ory Kratos, enhancing security and user experience.
- The ability to bypass the logout consent screen for specific clients, streamlining the logout process.
- Simplified migration with the new feature to import OAuth2 Client IDs, making the transition to Ory Hydra smoother.
- Support for the OIDC Verifiable Credentials specification, expanding the server's capabilities in identity verification.
Thank all contributors who have made this release available!
Bug Fixes
-
Return empty slice if requested_scope or audience is null (#3711) (65165e7)
-
Correct id token type in token exchange response (#3625) (d1f9ba8):
-
Handle subject mismatch gracefully (#3619) (af0d477):
We now redirect to the original request URL if the subjects between the remembered Hydra session and what was confirmed by the login screen does not match.
-
Handle token hook auth config (#3677) (1a40833):
- fix: handle token hook auth config
- fix: bump golangci-lint
-
Incorrect down migration (#3708) (8812e0e), closes /github.com/ory/hydra/pull/3705#discussion_r1471514014
-
Timeout in jwt-bearer grants when too many grants are available (#3692) (a748797)
-
Deflake ttl test (6741a49)
-
Only query access tokens by hashed signature (a21e945)
-
Reject invalid JWKS in client configuration / dependency cleanup and bump (#3603) (1d73d83)
-
Restore ability to override auth and token urls for exemplary app (#3590) (dfb129a)
-
Return proper error when the grant request cannot be parsed (#3558) (26f2d34)
Documentation
Features
-
Add prompt=registration (#3636) (19857d2):
Ory Hydra now supports a
registrationvalue for thepromptparameter of the authorization request. When specifyingprompt=registration, Ory Hydra will redirect the user to the URL found underurls.registration(instead ofurls.login). -
Add skip_logout_consent option to clients (#3705) (2a653e6):
Adds a special field which disables the logout consent screen when performing OIDC logout.
-
Re-enable legacy client IDs (#3628) (5dd7d30):
This patch changes the primary key of the
hydra_clienttable. We do not expect issues, as that table is probably not overly huge in any deployment. We do however highly recommend to test the migration performance on a staging environment with a similar database setup. -
Remove flow cookie (#3639) (cde3a30):
This patch removes the flow cookie. All information is already tracked in the request query parameters as part of the {login|consent}_{challenge|verifier}.
-
Remove login session cookie during consent flow (#3667) (5f41949)
-
Add more resolution to events and collect client metrics (#3568) (466e66b)
-
Add state override (b8b9154)
-
Add support for OIDC VC (#3575) (219a7c0):
This adds initial support for issuing verifiable credentials as specified in https://openid.net/specs/openid-connect-userinfo-vc-1_0.html.
Because the spec is still in draft, public identifiers are suffixed with
draft_00. -
Allow to disable claim mirroring (#3563) (c72a316):
This PR introduces another config option called
oauth2:mirror_top_level_claimswhich may be used to disable the mirroring of custom claims into theextclaim of the jwt. This new config option is an opt-in. If unused the behavior remains as-is to ensure backwards compatibility.Example:
oauth2: allowed_top_level_claims: - test_claim mirror_top_level_claims: false # -> this will prevent test_claim to be mirrored within ext -
Bump fosite and add some more tracing (0b56f53)
-
cmd: Add route that redirects to the auth code url (4db6416)
-
Propagate logout to identity provider (#3596) (c004fee):
- feat: propagate logout to identity provider
This commit improves the integration between Hydra and Kratos when logging out the user.
This adds a new configuration key for configuring a Kratos admin URL. Additionally, Kratos can send a session ID when accepting a login request. If a session ID was specified and a Kratos admin URL was configured, Hydra will disable the corresponding Kratos session through the admin API if a frontchannel or backchannel logout was triggered.
- fix: add special case for MySQL
- chore: update sdk
- chore: consistent naming
- fix: cleanup persister
-
Support different jwt scope claim strategies (#3531) (45da11e)
Changelog
- b346f90e autogen(docs): generate and bump docs
- 01aeffc6 autogen(docs): regenerate and update changelog
- 3a65840d autogen(docs): regenerate and update changelog
- 2dc52b4d autogen(docs): regenerate and update changelog
- 74732591 autogen(docs): regenerate and update changelog
- 4b8c9715 autogen(docs): regenerate and update changelog
- d0dfc0f0 autogen(docs): regenerate and update changelog
- 9e9be2d2 autogen(docs): regenerate and update changelog
- ada59a5f autogen(docs): regenerate and update changelog
- cdd2647c autogen(docs): regenerate and update changelog
- e4c160f5 autogen(docs): regenerate and update changelog
- 5121dba3 autogen(docs): regenerate and update changelog
- 21e0a9bd autogen(docs): regenerate and update changelog
- 89b1b1bd autogen(docs): regenerate and update changelog
- 0a5e0439 autogen(docs): regenerate and update changelog
- 6cbe0893 autogen(docs): regenerate and update changelog
- 78617027 autogen(docs): regenerate and update changelog
- c9f4b5f3 autogen(docs): regenerate and update changelog
- fe260d10 autogen(docs): regenerate and update changelog
- fbf39dd3 autogen(docs): regenerate and update changelog
- 9b33fc55 autogen(docs): regenerate and update changelog
- f9cee328 autogen(docs): regenerate and update changelog
- 841d58b8 autogen(docs): regenerate and update changelog
- 4a8e9a4c autogen(docs): regenerate and update changelog
- cdc0bec3 autogen(openapi): regenerate swagger spec and internal client
- 4a00e3e0 autogen(openapi): regenerate swagger spec and internal client
- dedcf5b4 autogen(openapi): regenerate swagger spec and internal client
- 92eb03a0 autogen(openapi): regenerate swagger spec and internal client
- f9a87d35 autogen(openapi): regenerate swagger spec and internal client
- 1ff8f20a autogen(openapi): regenerate swagger spec and internal client
- 11bf9df8 autogen(openapi): regenerate swagger spec and internal client
- e7968931 autogen(openapi): regenerate swagger spec and internal client
- 27f2ef50 autogen(openapi): regenerate swagger spec and internal client
- 35d62950 autogen(openapi): regenerate swagger spec and internal client
- ce00a428 autogen(openapi): regenerate swagger spec and internal client
- db4fd7d1 autogen(openapi): regenerate swagger spec and internal client
- 146b1625 autogen(openapi): regenerate swagger spec and internal client
- e1636d1e autogen(openapi): regenerate swagger spec and internal client
- 9389773a autogen(openapi): regenerate swagger spec and internal client
- af859fe4 autogen(openapi): regenerate swagger spec and internal client
- f1708f2a autogen(openapi): regenerate swagger spec and internal client
- 3e8413e9 autogen(openapi): regenerate swagger spec and internal client
- 11c8c724 autogen(openapi): regenerate swagger spec and internal client
- 800ce0a1 autogen: add v2.2.0-rc.3 to version.schema.json
- 8168ee31 autogen: pin v2.2.0-pre.1 release commit
- 04872174 autogen: render config schema
- a0c06ecb chore(deps): bump @cypress/request and cypress (#3641)
- b177f81a chore(deps): bump axios and @openapitools/openapi-generator-cli (#3701)
- 23c81943 chore(deps): bump debug from 3.2.6 to 3.2.7 (#3640)
- 18d97936 chore(deps): bump follow-redirects in /test/e2e/oauth2-client (#3697)
- 4fa28890 chore(deps): bump github.com/docker/docker (#3707)
- 2ba35473 chore(deps): bump golang.org/x/crypto from 0.15.0 to 0.17.0 (#3680)
- efc00a8b chore(deps): bump golang.org/x/net from 0.14.0 to 0.17.0 (#3645)
- 083c90de chore: build tag (#3613)
- 3615e3df chore: bump docker base images (#3632)
- aa8a364e chore: bump openapi-generator (#3696)
- 2dc66061 chore: improve context (#3656)
- 8e949299 chore: update otel (#3686)
- f0501d2c docs: fix typo (#3649)
- f502d6e3 feat: add --skip-logout-consent flag to CLI (#3709)
- 5c8e7923 feat: add authentication options to hooks (#3633)
- 62c006b9 feat: add flag to export public keys (#3684)
- 39ee5e1f feat: add missing index for jwk table (#3691)
- 19857d20 feat: add prompt=registration (#3636)
- 2a653e66 feat: add skip_logout_consent option to clients (#3705)
- 88b0b7cf feat: allow injecting extra fosite strategies (#3646)
- 5dd7d306 feat: re-enable legacy client IDs (#3628)
- cde3a30a feat: remove flow cookie (#3639)
- 5f41949a feat: remove login session cookie during consent flow (#3667)
- 95cc2735 feat: support multiple token URLs (#3676)
- d1f9ba8e fix: correct id token type in token exchange response (#3625)
- 22f0119a fix: dropped persistence/sql test errors (#3670)
- 5133cf97 fix: handle logout double-submit gracefully (#3675)
- af0d477e fix: handle subject mismatch gracefully (#3619)
- 1a40833e fix: handle token hook auth config (#3677)
- 24c3be57 fix: improved SSRF protection (#3669)
- 8812e0e6 fix: incorrect down migration (#3708)
- 3a764a05 fix: remove required mark (#3693)
- a7487977 fix: timeout in jwt-bearer grants when too many grants are available (#3692)
- 0176adc1 fix: verifiable credentials JWT format (#3614)
- 8e6c4bfa autogen(docs): regenerate and update changelog
- 33950db8 autogen(docs): regenerate and update changelog
- 28e9e31b autogen(openapi): regenerate swagger spec and internal client
- 57096be9 autogen: pin v2.2.0 release commit
- bfc05d00 chore(deps): bump github.com/opencontainers/runc from 1.1.8 to 1.1.12 (#3710)
- 65165e77 fix: return empty slice if requested_scope or audience is null (#3711)
Artifacts can be verified with cosign using this public key.
v2.2.0-rc.3
8 months agoIntroduces logout compatibility with Ory Kratos.
Bug Fixes
- Add exceptions for internal IP addresses (#3608) (1f1121c)
- Add kid to verifiable credential header (#3606) (9f1c8d1)
- Deflake ttl test (6741a49)
- Docker build (#3609) (01ff9da)
- Enable CORS with hot-reloaded origins (#3601) (6f592fc)
- Only query access tokens by hashed signature (a21e945)
- Racy random string generation (#3555) (1b26c4c)
- Reject invalid JWKS in client configuration / dependency cleanup and bump (#3603) (1d73d83)
- Restore ability to override auth and token urls for exemplary app (#3590) (dfb129a)
- Return proper error when the grant request cannot be parsed (#3558) (26f2d34)
- Use correct tracer in middleware (#3567) (807cbd2)
Code Generation
- Pin v2.2.0-rc.3 release commit (ad8a4ba)
Features
-
Add more resolution to events and collect client metrics (#3568) (466e66b)
-
Add state override (b8b9154)
-
Add support for OIDC VC (#3575) (219a7c0):
This adds initial support for issuing verifiable credentials as specified in https://openid.net/specs/openid-connect-userinfo-vc-1_0.html.
Because the spec is still in draft, public identifiers are suffixed with
draft_00. -
Allow to disable claim mirroring (#3563) (c72a316):
This PR introduces another config option called
oauth2:mirror_top_level_claimswhich may be used to disable the mirroring of custom claims into theextclaim of the jwt. This new config option is an opt-in. If unused the behavior remains as-is to ensure backwards compatibility.Example:
oauth2: allowed_top_level_claims: - test_claim mirror_top_level_claims: false # -> this will prevent test_claim to be mirrored within ext -
Bump fosite and add some more tracing (0b56f53)
-
cmd: Add route that redirects to the auth code url (4db6416)
-
Propagate logout to identity provider (#3596) (c004fee):
- feat: propagate logout to identity provider
This commit improves the integration between Hydra and Kratos when logging out the user.
This adds a new configuration key for configuring a Kratos admin URL. Additionally, Kratos can send a session ID when accepting a login request. If a session ID was specified and a Kratos admin URL was configured, Hydra will disable the corresponding Kratos session through the admin API if a frontchannel or backchannel logout was triggered.
- fix: add special case for MySQL
- chore: update sdk
- chore: consistent naming
- fix: cleanup persister
-
Support different jwt scope claim strategies (#3531) (45da11e)
Changelog
- 2c452efd autogen(docs): regenerate and update changelog
- 551c359d autogen(docs): regenerate and update changelog
- 93ebaee6 autogen(docs): regenerate and update changelog
- 7cfba846 autogen(docs): regenerate and update changelog
- cb647702 autogen(docs): regenerate and update changelog
- 938d4bba autogen(docs): regenerate and update changelog
- 0072ddf7 autogen(docs): regenerate and update changelog
- c30de7f8 autogen(docs): regenerate and update changelog
- 6c298b2f autogen(docs): regenerate and update changelog
- a547a749 autogen(docs): regenerate and update changelog
- 5704640c autogen(docs): regenerate and update changelog
- e586cc2c autogen(docs): regenerate and update changelog
- 2bdad2c2 autogen(docs): regenerate and update changelog
- dc878b82 autogen(docs): regenerate and update changelog
- 425c977a autogen(docs): regenerate and update changelog
- 339bf40e autogen(docs): regenerate and update changelog
- ea40d443 autogen(docs): regenerate and update changelog
- 71d18536 autogen(docs): regenerate and update changelog
- be85c29a autogen(docs): regenerate and update changelog
- 598c21d7 autogen(docs): regenerate and update changelog
- 42a9615a autogen(docs): regenerate and update changelog
- 330530d7 autogen(openapi): regenerate swagger spec and internal client
- 254a21b2 autogen(openapi): regenerate swagger spec and internal client
- ad8a4bab autogen: pin v2.2.0-rc.3 release commit
- 6631c213 autogen: render config schema
- 59ec76ba chore(deps): bump semver from 5.7.0 to 5.7.2 (#3569)
- 9fd59e2b chore(deps): bump semver from 5.7.0 to 5.7.2 in /test/e2e/oauth2-client (#3570)
- 3c5c1265 chore(deps): bump tough-cookie, @cypress/request and wait-on (#3592)
- 48d5df43 chore: add hperl as codeowner (#3607)
- efd9ca7d chore: bump deps (#3560)
- d5099cbb chore: remove fosite branch override (#3599)
- 39145855 chore: replace fosite rewrite (#3564)
- 8ed2a2d3 chore: support in README (#3565)
- 1a1f5044 chore: update repository templates to https://github.com/ory/meta/commit/ac80097fa427e7ae39820c59cac62dc6e11b9aff
- eb89af7c chore: update repository templates to https://github.com/ory/meta/commit/af28aff50b62a9eeb69de4842e0e164f82c9e066
- 4db64161 feat(cmd): add route that redirects to the auth code url
- 749eb8db feat: add
hydra migrate statussubcommand (#3579) - 466e66bd feat: add more resolution to events and collect client metrics (#3568)
- b8b91540 feat: add state override
- 219a7c06 feat: add support for OIDC VC (#3575)
- 8eed3068 feat: allow Go migrations (#3602)
- 8900cbb7 feat: allow additional SQL migrations (#3587)
- c72a3164 feat: allow to disable claim mirroring (#3563)
- 0b56f53a feat: bump fosite and add some more tracing
- 5bd9002d feat: parallel generation of JSON web key set (#3561)
- c004fee6 feat: propagate logout to identity provider (#3596)
- 45da11e4 feat: support different jwt scope claim strategies (#3531)
- 1f1121ca fix: add exceptions for internal IP addresses (#3608)
- 9f1c8d19 fix: add kid to verifiable credential header (#3606)
- 6741a49f fix: deflake ttl test
- 01ff9da8 fix: docker build (#3609)
- 6f592fc8 fix: enable CORS with hot-reloaded origins (#3601)
- a21e9451 fix: only query access tokens by hashed signature
- 1b26c4cb fix: racy random string generation (#3555)
- 1d73d83e fix: reject invalid JWKS in client configuration / dependency cleanup and bump (#3603)
- dfb129a5 fix: restore ability to override auth and token urls for exemplary app (#3590)
- 26f2d344 fix: return proper error when the grant request cannot be parsed (#3558)
- 807cbd20 fix: use correct tracer in middleware (#3567)
Artifacts can be verified with cosign using this public key.
v2.2.0-pre.0
9 months agoTest release
Code Generation
- Pin v2.2.0-pre.0 release commit (116c1e8)
Features
Changelog
- be99edea autogen(docs): generate and bump docs
- 4877c59d autogen(docs): regenerate and update changelog
- 4b4c033e autogen(docs): regenerate and update changelog
- d4ad1073 autogen: add v2.2.0-rc.2 to version.schema.json
- 116c1e89 autogen: pin v2.2.0-pre.0 release commit
- 6a0be838 autogen: render config schema
- 47582578 chore: bump ory/x
- c1e1a569 feat: add distroless docker image (#3539)
- 44ed0ac8 feat: add event tracing (#3546)
Artifacts can be verified with cosign using this public key.
v2.2.0-rc.2
10 months agoThis release optimizes the performance of authorization code grant flows by minimizing the number of database queries. We acheive this by storing the flow in an AEAD-encoded cookie and AEAD-encoded request parameters for the authentication and consent screens.
BREAKING CHANGE:
- The client that is used as part of the authorization grant flow is stored in the AEAD-encoding. Therefore, running flows will not observe updates to the client after they were started.
- Because the login and consent challenge values now include the AEAD-encoded flow, their size increased to around 1kB for a flow without any metadata (and increases linearly with the amount of metadata). Please adjust your ingress / gateway accordingly.
Bug Fixes
- Version clash in apk install (24ebdd3)
Code Generation
- Pin v2.2.0-rc.2 release commit (b183040)
Features
Changelog
- 4194d750 autogen(docs): regenerate and update changelog
- 898aa001 autogen(docs): regenerate and update changelog
- b183040a autogen: pin v2.2.0-rc.2 release commit
- a8ecf807 feat: hot-reload Oauth2 CORS settings (#3537)
- 3ec683d7 feat: sqa metrics v2 (#3533)
- 24ebdd3f fix: version clash in apk install
Artifacts can be verified with cosign using this public key.
v2.1.2
10 months agoWe are excited to announce the next Ory Hydra release! This release includes the following important changes:
- Fixed a memory leak in the OpenTelemetry implementation, improving overall memory usage and stability.
- Added a missing index for faster janitor cleanup, resulting in quicker and more efficient cleanup operations.
- Fixed a bug related to SameSite in dev mode, ensuring proper functionality and consistency in handling SameSite attributes during development.
We appreciate your continuous support and feedback. Please feel free to reach out to us with any further suggestions or issues.
Bug Fixes
-
Add index on requested_at for refresh tokens and use it in janitor (#3516) (5b8e712)
-
Do not use prepared SQL statements and bump deps (#3506) (31b9e66)
-
sql: Incorrect JWK query (#3499) (13ce0d6):
persister_grant_jwkhad an OR statement without bracket leading to not using the last part of the query.
Code Generation
- Pin v2.1.2 release commit (d94ed6e)
Documentation
Features
Changelog
- 0e84c241 autogen(docs): generate and bump docs
- 9f371723 autogen(docs): regenerate and update changelog
- 872720b3 autogen(docs): regenerate and update changelog
- 49072237 autogen(docs): regenerate and update changelog
- ba45af00 autogen(docs): regenerate and update changelog
- 3703e5a7 autogen(docs): regenerate and update changelog
- ca85a170 autogen(docs): regenerate and update changelog
- 0e7e95fc autogen(docs): regenerate and update changelog
- be8f7266 autogen: add v2.1.1 to version.schema.json
- d94ed6e4 autogen: pin v2.1.2 release commit
- 20c6fa76 autogen: render config schema
- 400b9af0 chore(deps): bump @nestjs/core and @openapitools/openapi-generator-cli (#3493)
- f2f007db chore(deps): bump github.com/docker/distribution (#3514)
- b69a332b chore: bump ory/x (#3518)
- cf20054f chore: remove unneeded dependency (#3494)
- e2b7665c chore: update nodemon version for oauth2 client (#3503)
- b71a36bf docs: incorrect json output format example (#3497)
- 083d518c feat: add --skip-consent flag to hydra cli (#3492)
- 13ce0d6f fix(sql): incorrect JWK query (#3499)
- 5b8e7121 fix: add index on requested_at for refresh tokens and use it in janitor (#3516)
- eddf7f38 fix: disable health check request logs (#3496)
- 31b9e663 fix: do not use prepared SQL statements and bump deps (#3506)
- 5751fae7 fix: proper SameSite=None in dev mode (#3502)
- 1b1899e9 fix: sqa config values unified across projects (#3490)
Artifacts can be verified with cosign using this public key.
v2.1.1
1 year agoWe are excited to share this year's Q1 release of Ory Hydra: v2.1!
Highlights:
- Support for Datadog tracing (#3431).
- Ability to skip consent for trusted clients (#3451).
- Setting access token type in the OAuth2 Client is now possible (#3446).
- Revoke login sessions by SessionID (#3450).
- Session lifespan extended on session refresh (#3464).
- Token request hooks added for all grant types (#3427).
- Reduced SQL tracing noise (#3481).
Don't want to run the upgrade yourself? Switch to Ory Network!
Bug Fixes
- Double-hashed access token signatures (#3486) (8720b25), closes #3485
- Reduce SQL tracing noise (#3481) (6e1f545)
Code Generation
- Pin v2.1.1 release commit (6efae7c)
Changelog
- df16a26c autogen(docs): generate and bump docs
- ed2ac06b autogen(docs): regenerate and update changelog
- 6078f85a autogen(docs): regenerate and update changelog
- ddfbd659 autogen: add v2.1.0 to version.schema.json
- 6efae7cf autogen: pin v2.1.1 release commit
- ad549d61 autogen: pin v2.1.1 release commit
- 2f7cda5f autogen: render config schema
- 0448284f chore: update ory/x (#3480)
- 8720b250 fix: double-hashed access token signatures (#3486)
- 6e1f5454 fix: reduce SQL tracing noise (#3481)
Artifacts can be verified with cosign using this public key.
v2.1.0
1 year agoWe are excited to share this year's Q1 release of Ory Hydra: v2.1.0!
Highlights:
- Support for Datadog tracing (#3431).
- Ability to skip consent for trusted clients (#3451).
- Setting access token type in the OAuth2 Client is now possible (#3446).
- Revoke login sessions by SessionID (#3450).
- Session lifespan extended on session refresh (#3464).
- Token request hooks added for all grant types (#3427).
- Reduced SQL tracing noise (#3481).
Don't want to run the upgrade yourself? Switch to Ory Network!
Bug Fixes
Code Generation
- Pin v2.1.0 release commit (3649832)
Changelog
- 5c2e2271 autogen(docs): regenerate and update changelog
- 36498324 autogen: pin v2.1.0 release commit
- 6e1f5454 fix: reduce SQL tracing noise (#3481)
Artifacts can be verified with cosign using this public key.
v2.1.0-pre.2
1 year agoautogen: pin v2.1.0-pre.2 release commit
Code Generation
- Pin v2.1.0-pre.2 release commit (3b1d87e)
Changelog
- 3b1d87e3 autogen: pin v2.1.0-pre.2 release commit
Artifacts can be verified with cosign using this public key.
v2.1.0-pre.1
1 year agoautogen: pin v2.1.0-pre.1 release commit
Code Generation
- Pin v2.1.0-pre.1 release commit (2289e6b)
Changelog
- 2289e6b8 autogen: pin v2.1.0-pre.1 release commit
- 0d740d9d chore(deps): bump github.com/opencontainers/runc from 1.1.4 to 1.1.5 (#3476)
- c29b9680 chore: update alpine version
Artifacts can be verified with cosign using this public key.
v2.0.3
1 year agoBugfixes for migration and pagination regressions and a new endpoint.
Bug Fixes
-
Add
client_idandclient_secrettorevokeOAuth2Token(#3373) (93bac07) -
Docker build (48217bd)
-
Invalidate tokens with inconsistent state (#3385) (542ea77), closes #3346:
This patch includes SQL migrations targeting environments which have not yet migrated to Ory Hydra 2.0. It removes inconsistent records which resolves issues during the migrations process. Please be aware that some users might be affected by this change. They might need to re-authorize certain apps. However, most active records should not be affected by this.
Installations already on Ory Hydra 2.0 will not be affected by this change.
-
No longer auto-generate system secret (c5fe043):
This patch changes Ory Hydra's behavior to no longer auto-generate a temporary secret when no global secret was set. The APIs now return an error instead.
-
Prevent multiple redirections to post logout url (#3366) (50666b9), closes #3342
Code Generation
- Pin v2.0.3 release commit (16831c5)
Features
Changelog
- 5d79e57a autogen(docs): generate and bump docs
- bd190868 autogen(docs): regenerate and update changelog
- 2720839b autogen(docs): regenerate and update changelog
- a400a354 autogen(docs): regenerate and update changelog
- 6710ddc4 autogen(docs): regenerate and update changelog
- d7a28e94 autogen(docs): regenerate and update changelog
- f2925ee4 autogen(docs): regenerate and update changelog
- 2986605e autogen(docs): regenerate and update changelog
- c586e035 autogen(openapi): regenerate swagger spec and internal client
- c65342e2 autogen: add v2.0.2 to version.schema.json
- 16831c55 autogen: pin v2.0.3 release commit
- b28bad38 chore(deps): bump decode-uri-component in /test/e2e/oauth2-client (#3377)
- cb23cca0 chore(deps): bump minimatch in /test/e2e/oauth2-client (#3381)
- 93fc0a1b chore(deps): bump qs from 6.5.2 to 6.5.3 (#3380)
- 316b5820 chore(deps): bump qs, body-parser and express in /test/e2e/oauth2-client (#3379)
- f9f0337f chore: list contributors in file (#3345)
- d275ad66 feat: list consent sessions by session id (#2853)
- 93bac074 fix: add
client_idandclient_secrettorevokeOAuth2Token(#3373) - 48217bd2 fix: docker build
- 4ee4456d fix: introspect command CLI example (#3353)
- 542ea771 fix: invalidate tokens with inconsistent state (#3385)
- c5fe0433 fix: no longer auto-generate system secret
- 50666b96 fix: prevent multiple redirections to post logout url (#3366)
- 3831b448 fix: strip
publicfrom schema (#3374) - e8d8de90 fix: token pagination (#3384)
Artifacts can be verified with cosign using this public key.